Introduction
Welcome to Part 2 of my 5 Part blog series, “How To Break Into DFIR”. Part 2 will focus on understanding the basics of Windows Forensics, primarily from an artifact knowledge perspective, and what resources you should focus on to get this understanding. Most of what I’m going to share are the resources I used when I was in the process of getting my feet wet in Digital Forensics and Incident Response (DFIR) and I found them to be very helpful. What I do want to emphasize though is these resources that I share will be more beneficial if followed in the particular order that I list so there is natural progression with your learning and so you don’t become too overwhelmed at the start of your journey.
Step 1 – Watch 13Cubed’s YouTube Playlist – Introduction To Windows Forensics
It wouldn’t be an intro to Windows Forensics blog without mentioning one of the best Windows Forensics resources out there and that is 13Cubed’s YouTube Channel run by Richard Davis. Like many of my current peers, this is where I got my start in learning about Windows Forensics and obtaining artifact knowledge. Back in 2020, I started to watch 13Cubed’s videos to really start understanding the basic concepts of Windows Forensics and I was blown away by the content he was providing for free. Fast forward to now, and anytime someone asks me where do I start learning Windows Forensics, I always point them to 13Cubed’s YouTube playlist, Introduction To Windows Forensics.
As of this writing, this playlist consists of 22 videos, each covering a particular Windows Forensics artifact or topic, culminating in the final video where Richard introduces his paid training courses. More on that later! Windows artifact knowledge is a crucial first step into becoming a successful DFIR practitioner, but it requires a lot of patience. There are simply too many Windows artifacts that exist to fully understand them all at an expert level in short order, but having a basic understanding of the most important artifacts will prove highly beneficial as you begin your DFIR career.
Step 2 – Windows Forensics Cheat Sheets
This takes us to step 2 which is leveraging the many Windows Forensics cheat sheets that are freely available. These become extremely handy once you have a basic understanding of the most important artifacts because again, there are simply so many artifacts, so having these cheat sheets available at your disposal is highly recommended. There is no shame in using cheat sheets while you begin your DFIR career, and you will become so familiar with many artifacts that eventually you won’t need to rely on these cheat sheets anymore. Here is a list of some of the best cheat sheets for Windows Forensics (Be sure to keep these links handy):
- 13Cubed Window Forensics Cheat Sheets
- SANS Cheat Sheets and DFIR Posters
- Microsoft’s Guidance for Incident Responders Blog Post
- Blue Cape Security Practical Windows Forensics Cheat Sheet
- CyberDefenders Windows Forensics Cheat Sheet
Step 3 – Watch 13Cubed Video – What’s on My DFIR Box?
Now the fun part! By the time you reach Step 3, you should have taken a few months (typically 2-3 months) to really absorb all of the material from Step 1 and Step 2 before diving into this next step. This is a very important step in the process, as you will now start to gain some hands-on experience before even stepping into a DFIR role. However, before diving into the actual hands-on material, you need to start downloading forensic tools onto your personal workstation. It is highly recommended to have a fully dedicated workstation where your forensic tools and resources will be stored. I personally built my own PC which has 128GB of RAM and 3 NVMe Gen4 SSDs (1TB SSD as the OS Drive, 2 2TB SSDs for my tools and resources), but you do not need this much RAM or storage – 64GB of RAM and at least 1 2TB SSD is more than enough storage outside of your OS Drive.
13Cubed’s YouTube video, What’s on My DFIR Box? is the next resource you should leverage to fully understand what are some of the key tools you should get familiar with as you start your DFIR journey. In this video, Richard also goes over the specs of his personal workstation for your reference. Some of the tools highlighted in this video are Windows Subsystem for Linux (WSL) 2, FTK Imager, Arsenal Image Mounter (AIM), Kroll Artifact Parser and Extractor (KAPE), Eric Zimmerman Tools, and more. The best part is most of these tools are open source!
Step 4 – Create CyberDefenders Account and Complete Some Windows Forensics Labs
Step 4 is where you finally begin to dive into some hands-on labs to start practicing working with real data. I found CyberDefenders to be the best hand-on training platform out there that has a robust free tier called “Community” under the “Content” section. This can be found in the “Practice” section under the “CyberRange” dropdown. See the image below:

Once you are filtered on the “Community” content, the best place to start on CyberDefenders if you are wanting to get hands on experience with Windows Forensics labs, is to filter on “Windows” under the “Operating System” section, and “Endpoint Forensics” under the “Category” section. See the image below:
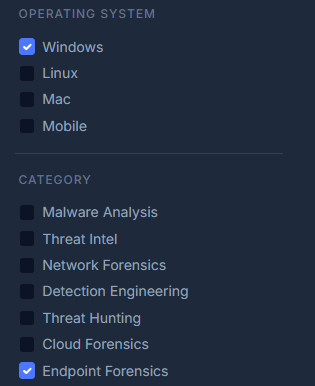
Here you will find many Windows Forensics labs that are focused on endpoint forensics or, as others call it, host forensics. The first lab I personally ever worked on was the Szechaun Sauce lab which I highly recommend. This lab, along with many others will give you the hands-on experience you need to feel confident heading into your first set of interviews in the near future.
Step 5 – Complete 13Cubed Course and Certification – Investigating Windows Endpoints
Now time for some formalized training. After obtaining artifact knowledge, downloading tools and resources on your workstation, and gaining some hands-on experience with CyberDefenders, the next natural step in the process is to get a certification through formalized training. This is a topic that always comes up when talking with folks in the industry. Training can be very costly, especially for those who just finished college and can’t afford thousands of dollars on training to be able to land a DFIR job. One cheaper alternative that I can’t speak highly enough of is 13Cubed’s Investigating Windows Endpoints course. It currently includes 40 lessons along with 365-day access. Once you finish this course, you will have the opportunity to take a knowledge assessment and earn the certification.
At the time of this writing, 13Cubed’s “Investigating Windows Endpoints” course is priced at $795 USD. I know for most this can seem very expensive, but it is a worthwhile investment in the early part of your career as you look into landing that first DFIR role. You will have such a major advantage when it comes to being prepared during the interview phase of the process, that the investment will pay for itself once you’re able to land the role. It also will demonstrate to hiring teams how serious and passionate you are about kickstarting your DFIR career that you will have a higher chance of getting an entry level role than most.
Step 6 – Apply for Entry Level DFIR Jobs
Arguably the most stressful step in this entire blog post is the job seeking and interview phase. By the time you reach this step, you should have been able to build a solid foundation of artifact knowledge, hands-on technical skills, formalized training, and a certification to go along with it all to feel fully confident in landing your first DFIR role! However, most early career professionals don’t know the market well – meaning what companies are looking to hire entry level individuals fresh out of college. Some companies require previous DFIR experience, while others are more flexible in hiring entry level candidates.
Luckily, I maintain one of the most comprehensive DFIR job boards out there and recommend you use this board to help guide you in what roles would be most realistic for you to pursue. This jobs board is fully maintained and updated on a weekly basis so you will always find the latest and greatest DFIR jobs on the market. You will see jobs categorized as “Internship”, “Entry-Level”, “Mid-Senior”, and “Leadership” so focus on applying to “Internships” and “Entry-Level”. Don’t worry about the internships being paid or not. All jobs on this board have salary information as those are the jobs that make it onto this board. You can find the DFIR Jobs board here!
Step 7 – Complete SANS Course FOR500: Windows Forensic Analysis and Obtain the GCFE certification
Similar to 13Cubed’s “Investigating Windows Endpoints” course, FOR500: Windows Forensic Analysis is yet another formalized training opportunity that will better prepare you to be a bona fide DFIR practitioner. This course dives into the following topics: Browser Forensic Artifacts, Browser Structure and Analysis, Cloud, Storage Analysis, Digital Forensic Fundamentals, Email Analysis, Event Log Analysis, File and Program Analysis, Forensic Artifact Techniques, System and Device Analysis, and User Artifact Analysis. Once the course is over, you will have the opportunity to become certified by obtaining the GIAC Certified Forensic Examiner (GCFE) certification. Having this SANS training and GIAC certification under your belt will just further deepen your understanding of Windows Forensics.
However, unlike the previous 6 steps outlined above, this step is dependent on some factors that might be out of your control. For starters, FOR500 by SANS is priced at around $8,780 USD without the GCFE certification which adds another $999 USD to the final total. However, some employers provide this training to their employees early in their tenure. So, in order to pay for this course, you would need to have landed a DFIR role at a company that also has training opportunities included such as SANS. Now of course, this concern won’t apply to those that opted to enroll and complete either one of the two accelerated programs at the SANS Institute – Applied Cybersecurity Certificate (ACS) Program or Bachelor’s Degree in Applied Cybersecurity (BACS) Program that I highlighted in Part 1 of my 5 Part blog series as you would have completed FOR500 and obtained the GCFE certification at the conclusion one of these two programs.
Conclusion
As you have read through this blog post, you have been able to see there is a natural progression with each of the above outlined steps. The order of these steps was fully intended to help guide you through your journey in a way that is realistically paced for a successful breakthrough into DFIR. As long as you follow each step, and spend the right amount of time on them, you should have the necessary tools and resources at your disposal to succeed. Keep in mind, everyone learns at their own pace, and some have less time in their day to dedicate the number of hours necessary to successfully accomplish each step so be sure to spend the time you feel is aligned with your pace and makes sense for you.
The next blog in this 5-part series will focus on Windows Memory Forensics.